When vendor breaches hit the news, your risk shouldn’t.
See operating controls, audit evidence, and technical documentation your security team can verify—live. No slides. No marketing speak. Just transparent access to the security infrastructure protecting your most sensitive data.
What you’ll see in 20 minutes
- Live SFTP/SSH data‑transfer with encryption and logging
- Zero‑trust network segmentation and 24/7 SOC monitoring
- PCI‑compliant call flows with audit trails
- Disaster recovery evidence (RTO/RPO, failover tests)
Why teams choose TSI
Evidence over assurances. Controls you can verify. A partner that welcomes scrutiny.
Defense‑in‑depth, by design
Segmented zones, hardware‑key 2FA, and IDS/IPS reduce lateral movement and surface threats fast.
Independently verified
ISO 27001, PCI DSS 4.0 L1, and HITRUST CSF certification with artifacts available under NDA.
Transparent operations
Immutable logs, searchable audit trails, and walkthroughs designed for CISOs and security leaders.
Controls & Proof
Target RTO for critical operations
Target RPO • backup intervals
Availability target
Defense‑in‑depth, by design
SFTP/SSH with AES‑compatible encryption, certificate auth, IP allow‑listing, and immutable transfer logs.
Zero‑Trust Network
Segmented zones (SafeNet/DMZ/Production/Admin), continuous SIEM monitoring, automated quarantine.
PCI‑Compliant Call Flows
DTMF masking, secure IVR capture, and 100% recording with role‑based access & auditability.
Want to see the controls live?
Data protection starts at the transport layer
Every exchange travels through encrypted channels. Connections are restricted to approved certificates and IP ranges, and every transfer is logged with timestamps, user, and file metadata.
- Zero tolerance for insecure protocols (e.g., unencrypted FTP)
- Centralized SIEM dashboards monitor anomalies in real time
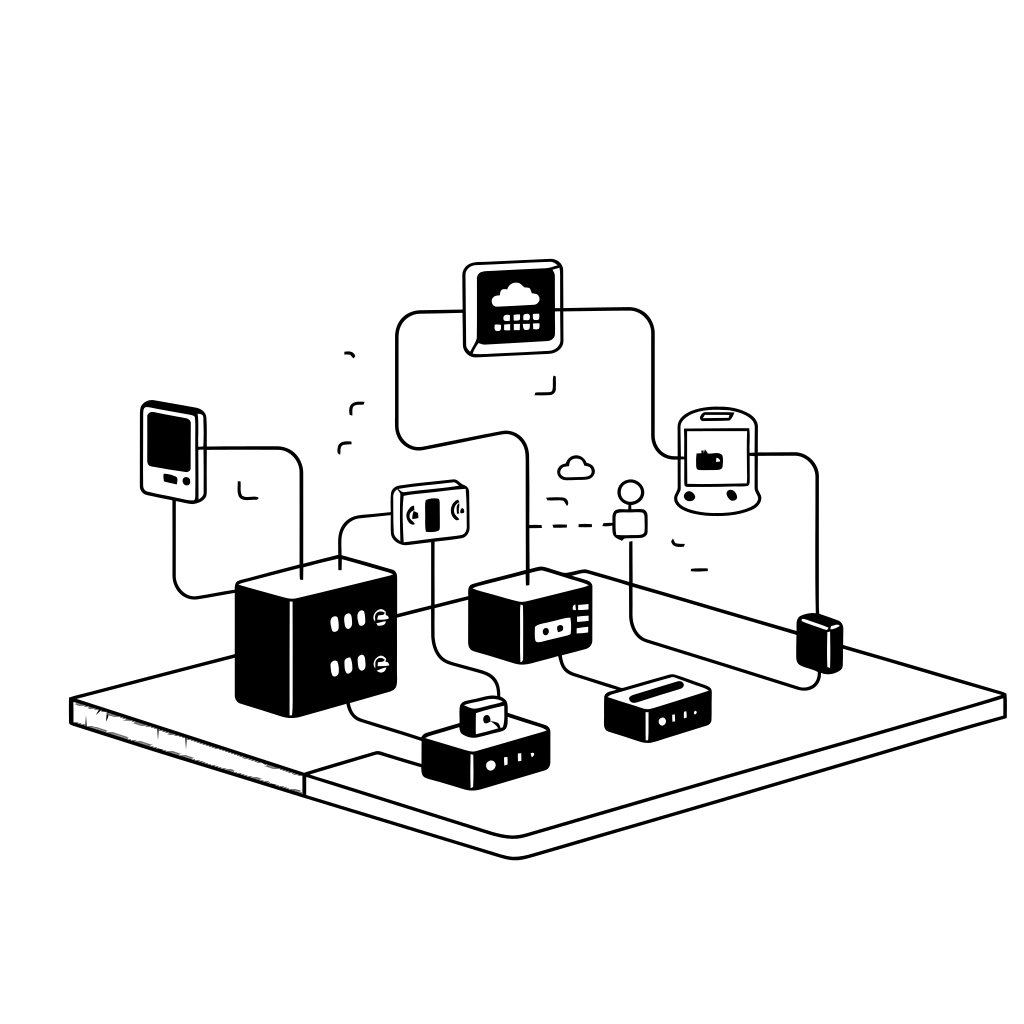
Data protection starts at the transport layer
Every exchange travels through encrypted channels. Connections are restricted to approved certificates and IP ranges, and every transfer is logged with timestamps, user, and file metadata.
- Zero tolerance for insecure protocols (e.g., unencrypted FTP)
- Centralized SIEM dashboards monitor anomalies in real time
Frequently asked
Do you have HITRUST certification?
Yes – TSI maintains HITRUST CSF (i1/r2) certification validated by an accredited third-party assessor. We’ll share our current certification letter, detailed control scope documentation, and implementation evidence during your security walkthrough.
Our HITRUST certification covers all systems processing PHI and PII, with annual recertification maintaining currency. We also provide inheritance documentation for clients pursuing their own HITRUST certification, potentially reducing your assessment scope and timeline.
How is data transferred and protected in transit?
All data exchanges use SFTP/SSH protocols with AES-compatible encryption. We do not accept unencrypted FTP, email attachments containing sensitive data, or insecure web uploads under any circumstances.
Access is controlled through certificate-based authentication and IP whitelisting. Each connection generates immutable logs including timestamps, authenticated user identities, transferred files, and transfer status. Our security team monitors these logs in real-time through SIEM dashboards that alert on anomalies
Do you pass independent third-party security audits?
Yes4TSI maintains multiple independent certifications including ISO 27001 for information security management, PCI DSS 4.0 Level 1 for payment card processing, and FISMA/ATO-aligned controls meeting federal standards.
Current audit reports, attestation letters, and certificates are available for review under mutual non-disclosure agreement. We provide these documents routinely during vendor risk assessments and can coordinate direct auditor-to-auditor communications when needed.
Where do you operate and can I visit facilities?
TSI operates across the United States through multiple secure facilities, each implementing consistent security controls validated through identical third-party audit procedures. Our distributed architecture provides geographic redundancy while maintaining unified security governance through centralized SOC monitoring.
We share specific facility locations and detailed security specifications during vendor assessments under appropriate confidentiality protections. Facility tours can be arranged for qualified prospects and clients following security briefing and visitor approval procedures.
Book a 20‑minute security walkthrough
We’ll tailor the session to your framework and evaluation criteria. Your information will only be used to coordinate the walkthrough.
© TSI. All rights reserved.
